Security
PAS 1192-5:2015
To understand the security requirements of a project reference should be made to PAS 1192-5:2015 Specification for security-minded building information modelling, digital built environments and smart asset management.
The specification has been developed to:
Address the steps required to create and cultivate an appropriate safety and security mindset and culture across many partners, including the need to monitor and audit compliance.
It outlines security threats to information during asset:
- Conception, strategy and briefing
- Procurement
- Design
- Construction
- Commissioning and handover
- Operation and maintenance
- Performance management
- Change of use/modification and
- Disposal/demolition
And it explains the need for trustworthiness and security controls to encompassing:
- Safety
- Authenticity
- Availability (including reliability)
- Confidentiality
- Integrity
- Possession
- Resilience and
- Utility
A useful place to start is to understand what security measures are required for a project. PAS 1192-5 provides a useful security triage process to indicate the likely level of security:
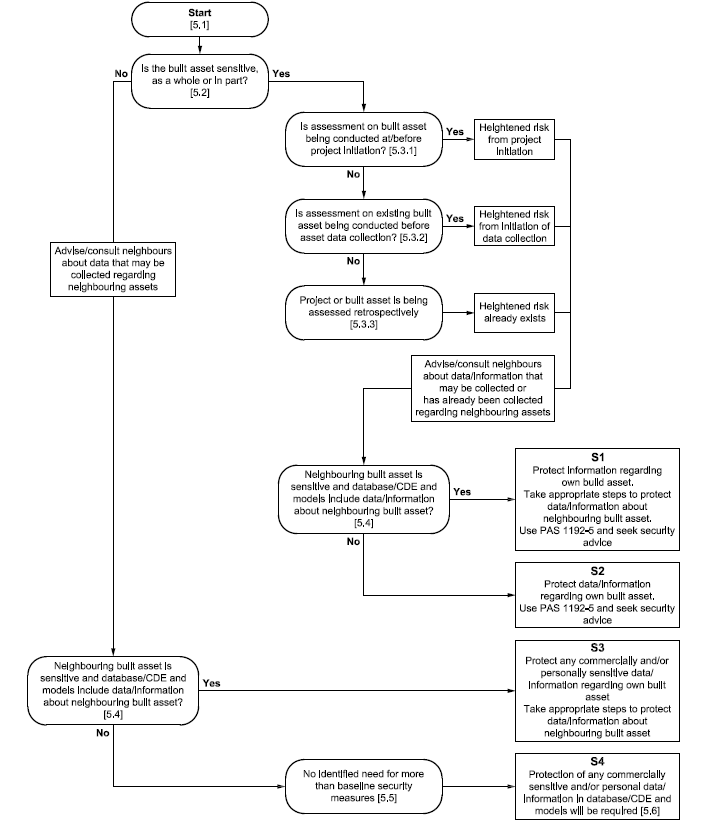
From PAS 1192-5:2015 – Figure 5
A Sensitive Built Asset
The first (and probably) the most important question is whether the built asset (either existing or proposed) is sensitive. PAS 1192-5 provides a list of examples where built assets would be defined as sensitive, most of the definitions are clear including:
- Designated under sections 128 or 129 or the Serious Organised Crime and Police Act 2005
- Fulfils a defence, law enforcement, national security or diplomatic function
But some are less clear and will require supporting evidence identifying why a built asset does or does not fall within categories such as:
- Is used or is planned to be used to host events of security significance
- Has been judged could be used to significantly compromise the integrity of the built asset as a whole, or its ability to function
It’s clear that the vast majority of built assets will not be sensitive and provided that there are no neighbouring sensitive built assets than a project will require S4 baseline security measures.
Baseline Security Measures
Baseline security measures should consist of steps to minimise threats arising from fraud, other criminal activities and cyber security incidents.
Although. it may be appropriate that a client or asset owner require a higher security than the recommended baseline security.
Cyber security good practice includes meeting the requirements of the Cyber Essentials Scheme. At the foundation level this requires a self-assessment of an organisations implementation of the Cyber Essentials controls which is the verified by an independent control body.
All UK Government suppliers should meet as a minimum the requirements of the Cyber Essentials Scheme and the Security Policy Framework.
A further consideration is the sensitivity of information that is exchanged through a project’s Common Data Environment for example if the data contains commercial information then the employer or asset owner should be clear of what information can be exchanged and who has access to the information to ensure that the flow of such information is controlled. The use of confidentiality and non-disclosure agreements can provide employers or asset owners with control over sensitive data.
Enhanced Security Measures
Where a project requires enhanced security beyond the baseline measures, PAS 1192-5 provides a framework for implementing the measures. This includes the development of a Built Asset Security Strategy (BASS), which leads onto a Built Asset Security Management Plan (BASMP) and then finally the Built Asset Security Information Requirements (BASIR). To provide more context each of these documents has an equivalent control document within PAS1192-2 and PAS1192-3:
| Asset Security | Asset | ||
| Business Strategy & Decision Making | Built Asset Security Strategy (BASS) | Which will link into: | Organisational Information Requirements (OIR) |
| Asset Delivery Definition | Built Asset Security Management Plan (BASMP) | Which will link into: | Asset Information Requirements (AMP) |
| Day-to-day delivery procedures | Built Asset Security Information Requirements (BASIR) | Which will link into: | Employer’s Information Requirements (EIR) |
Contents